Glossary
A comprehensive glossary of all things go-to-market, sales, and growth.
ABM Orchestration
ABM orchestration aligns marketing and sales actions across channels to deliver seamless, personalized experiences to high-value accounts.
Account
An account is a company or organization that you're targeting for sales. It can be a prospective, current, or even a past customer.
Account-Based Everything
Account-Based Everything (ABE) is a strategy aligning sales, marketing, and success teams to focus on a specific set of high-value accounts.
Account-Based Marketing
Account-Based Marketing (ABM) is a focused B2B strategy where marketing and sales collaborate to target and convert high-value accounts.
Account-Based Marketing Software
Account-Based Marketing (ABM) software helps teams coordinate personalized marketing and sales efforts to land high-value customer accounts.
Account-Based Sales
Account-Based Sales (ABS) is a focused B2B strategy where sales and marketing teams treat high-value accounts as individual markets of one.
Account-Based Sales Development
Account-Based Sales Development (ABSD) is a focused strategy where SDRs target key stakeholders within specific, high-value accounts.
Account-Based Selling
Account-Based Selling is a B2B strategy where sales and marketing treat high-value accounts as markets of one, using personalized outreach.
Account Development Representative
An Account Development Representative (ADR) identifies and qualifies new business opportunities, creating a pipeline for account executives.
Account Executive
An Account Executive (AE) is a sales professional responsible for closing new business deals and managing existing client relationships to drive revenue.
Account Management
Account management is the post-sales practice of building and nurturing long-term relationships with a company's most valuable clients.
Account Mapping
Account mapping is comparing your customer list with a partner's to find common prospects and unlock new sales opportunities.
Accounts Payable
Accounts Payable (AP) is the money a company owes its suppliers for goods or services bought on credit. It's listed as a current liability.
Affiliate Marketing
Affiliate marketing is a performance-based model where affiliates earn a commission for promoting another company’s products or services.
AI Data Enrichment
AI data enrichment uses artificial intelligence to automatically enhance and update raw data, making it more complete, accurate, and valuable.
AI Sales Agent
An AI sales agent is software that uses artificial intelligence to automate prospecting, outreach, and follow-up tasks traditionally handled by human sales representatives.
AI Sales Script Generator
An AI sales script generator is a tool that uses artificial intelligence to create personalized sales scripts for any outreach scenario.
Annual Recurring Revenue (ARR)
Annual Recurring Revenue (ARR) is the predictable income a company expects to receive from its customers over a one-year period.
API
An API (Application Programming Interface) is a software intermediary that allows two applications to talk to each other and exchange information.
Applicant Tracking System
An Applicant Tracking System (ATS) is a software application that manages your entire hiring and recruitment process from a single dashboard.
Application Performance Management
Application Performance Management (APM) monitors and manages an application's performance, availability, and the experience of its end-users.
Audience Targeting
Audience targeting is the process of segmenting consumers into specific groups to deliver more personalized and relevant marketing messages.
Average Revenue per User
Average Revenue per User (ARPU) is a key performance indicator that calculates the average revenue generated from each user or subscriber.
Awareness Buying Stage
The awareness stage is the first step in the buyer's journey, where a potential customer realizes they have a problem or an opportunity to explore.
B2B Data
Learn about B2B data, including sources and types of B2B data, leveraging B2B data for sales success, & ensuring the accuracy of B2B data.
B2B Data Enrichment
Learn about B2B data enrichment, including benefits of B2B data enrichment, implementing B2B data enrichment strategies, B2B data enrichment vs. data cleaning.
B2B Data Erosion
Learn about B2B data erosion, including causes of B2B data decay, strategies to combat data erosion, & measuring the impact of data erosion.
B2B Data Platform
Learn about B2B data platform, including key benefits of B2B data platforms, choosing the right B2B data platform, challenges in implementing B2B data platforms.
B2B Intent Data
Learn about B2B intent data, including how B2B intent data enhances sales strategies, sources of B2B intent data, leveraging B2B intent data for competitiveness.
B2B Intent Data Providers
Learn about B2B intent data providers, including evaluating intent data quality, leveraging intent data for growth, & B2B intent data: key providers comparison.
B2B Marketing Attribution
Learn about B2B marketing attribution, including challenges in B2B marketing attribution, & key metrics for effective attribution.
B2B Sales
Learn about B2B sales, including key strategies for B2B success, types of B2B sales models, & B2B vs. B2C sales: understanding the differences.
B2C2B
Learn about B2C2B, including how B2C2B transforms sales, key strategies for B2C2B success, & differences between B2C2B and B2B2C.
Behavioral Analytics
Learn about behavioral analytics, including implementing behavioral analytics successfully, & key metrics in behavioral analytics.
Big Data
Learn about big data, including understanding big data characteristics, benefits of leveraging big data, & challenges in managing big data.
Bottom of the Funnel
Learn about bottom of the funnel, including maximizing conversions at the funnel's end, & strategies for nurturing bottom-funnel leads.
Bounce Rate
Learn about bounce rate, including understanding bounce rate implications, key factors affecting bounce rate, & reducing your bounce rate effectively.
Brag Book
Learn about brag book, including crafting your outstanding brag book, essential components of a brag book, & brag book vs. resume: unveiling the differences.
Business Continuity
Learn about business continuity, including understanding key components, steps to ensure continuity, common challenges, & best practices.
Business Development Representative
Learn about business development representative, including skills and qualifications for BDRs, & roles and responsibilities of a BDR.
Business-to-Business (B2B)
Learn about B2B, including what is it, its key elements, the benefits of B2B partnerships, the differences between B2B and B2C, and strategies for effective marketing.
Buyer
Learn about buyer, including identifying your ideal buyer, understanding buyer's journey, & evaluating buyer decision processes.
Buyer Intent
Learn about buyer intent, including understanding buyer intent signals, strategies to capture buyer intent, & buyer intent vs. customer interest.
Buyer Intent Data
Learn about buyer intent data, including sourcing and interpreting buyer intent data, & key metrics in buyer intent analysis.
Buyer’s Remorse
Buyer’s remorse is the sense of regret or anxiety that can arise after making a purchase, often questioning if it was the right decision.
Buying Committee
A buying committee is a group of stakeholders within an organization who are jointly responsible for making major purchasing decisions.
Buying Criteria
Buying criteria are the specific requirements and standards a customer uses to evaluate products or services before making a decision.
Buying Intent
Buying intent is the collection of online cues and behaviors that signal a prospect is actively researching and moving toward a purchase decision.
Buying Signal
A buying signal is any action from a prospect that indicates they are interested in making a purchase, helping sales teams prioritize leads.
Call for Proposal
A Call for Proposal (CFP) is a document that solicits proposals, often through a bidding process, for a specific project or service.
Canary Releases
A canary release is a deployment strategy where new software is rolled out to a small user group first, minimizing risk before a full release.
Channel Partner
A channel partner is a company that works with a manufacturer or producer to market and sell their products, software, or services to customers.
Channel Partners
Channel partners are third-party firms that help market and sell a company's products or services, acting as an indirect sales force.
Chatbots
Chatbots are AI-powered programs that simulate human conversation. They interact with users via text or voice, typically for customer support.
Closed Lost
Closed Lost is a sales term for a deal that didn't go through. The prospect decided not to buy, or the sales team disqualified them.
Closed Opportunities
Closed opportunities are potential deals that have concluded. They are categorized as either 'closed-won' (a sale was made) or 'closed-lost'.
Closed Won
Closed Won is a CRM status for a sales deal that has been successfully concluded, resulting in a signed contract and a new customer.
Cohort Analysis
Cohort analysis is a behavioral analytics tool that groups users with common traits to track their actions and engagement over time.
Cold Calling
Cold calling is a sales tactic where reps contact potential customers by phone who haven't previously expressed interest in their product or service.
Cold Email
A cold email is an initial outreach sent to a potential customer with whom you've had no prior contact, aiming to introduce your business.
Cold Emailing
Cold emailing is sending unsolicited emails to potential customers you haven't contacted before, aiming to start a business conversation.
Commission
A commission is a service charge paid to an agent for a transaction. It's typically a percentage of the sale, rewarding performance directly.
Competitive Analysis
Competitive analysis means identifying your rivals and assessing their strategies to pinpoint your own business's strengths and weaknesses.
Competitive Intelligence (CI)
Competitive intelligence (CI) is the ethical gathering and analysis of market data to inform strategic business decisions and gain an advantage.
Consultative Selling
Consultative selling is an approach where salespeople act as expert advisors, diagnosing customer needs to provide the most suitable solutions.
Consumer
A consumer is an individual or entity that buys products or services for personal use, not for resale. They are the final user in a supply chain.
Consumer Relationship Management
Consumer Relationship Management (CRM) is a strategy for managing all of a company's relationships and interactions with its customers.
Contact Data
Contact data is the set of details, like names, emails, and phone numbers, used to get in touch with a person or business for outreach.
Contact Discovery
Contact discovery is the process of finding accurate contact details for potential leads, including names, emails, phone numbers, and job titles.
Content Management System
A Content Management System (CMS) is software for creating, managing, and modifying website content without needing specialized technical skills.
Content Rights Management
Content Rights Management involves controlling the use and distribution of copyrighted digital media to protect intellectual property.
Copyright Compliance
Copyright compliance is adhering to laws that protect creative works. It involves legally using content by obtaining permission or licenses.
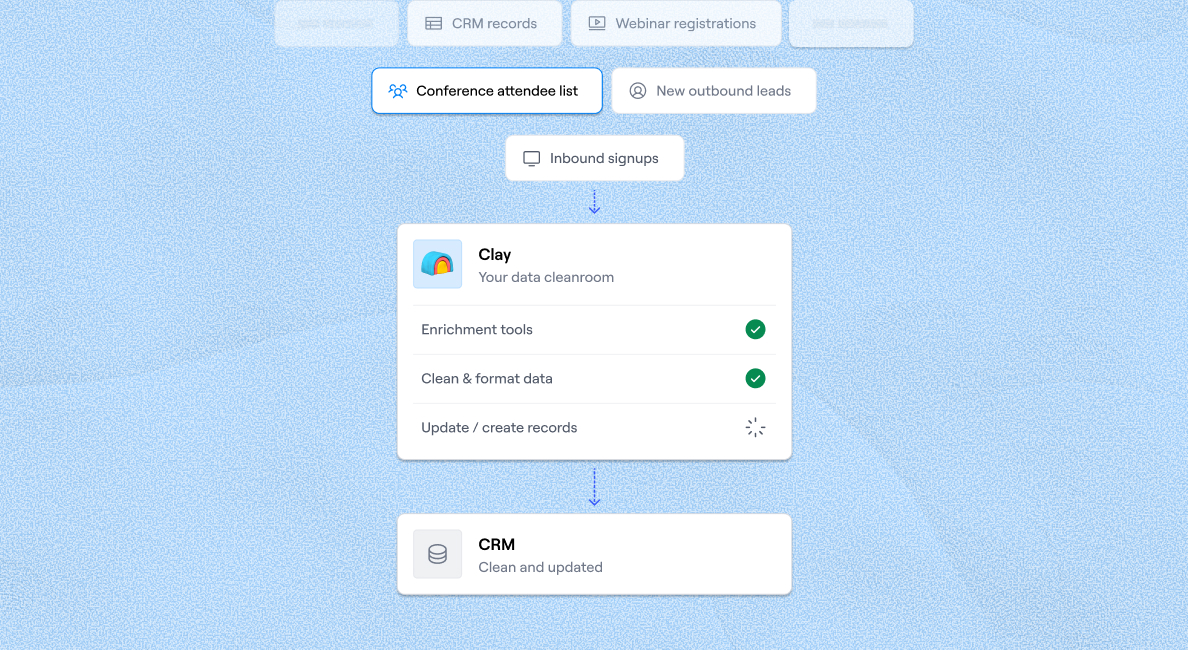
CRM Data Enrichment
CRM data enrichment is the process of enhancing existing customer records with additional, verified information to improve sales targeting, personalization, and overall data quality.
CRM Enrichment
CRM enrichment is the process of adding third-party data to your existing customer profiles to make them more complete and accurate.
CRM Integration
CRM integration connects your CRM software with other tools, creating a unified system for all your customer data and business processes.
Cross-Selling
Cross-selling is a sales tactic of encouraging customers to purchase products or services that are related to what they're already buying.
Cross-Site Scripting
Cross-Site Scripting (XSS) is a web security vulnerability that allows attackers to inject malicious scripts into trusted websites.
Custom API integration
A custom API integration is a bespoke connection between software, enabling them to communicate and share data to meet unique business requirements.
Customer Acquisition Cost
Customer Acquisition Cost (CAC) is the total cost a business spends to gain a new customer. It includes all sales and marketing expenses.
Customer Buying Signals
Customer buying signals are the actions, behaviors, or statements a prospect makes that indicate they are moving towards a purchase decision.
Customer Centricity
Customer centricity is a business approach that puts the customer at the heart of every decision, aiming to build loyalty and long-term value.
Customer Data Platform (CDP)
A Customer Data Platform (CDP) centralizes customer data from all sources to create a complete, unified profile for each individual customer.
Customer Relationship Management Systems
A Customer Relationship Management (CRM) system is a tool that centralizes customer data to help manage interactions and nurture relationships.
Customer Relationship Marketing
Customer relationship marketing is a strategy for building lasting connections with customers to foster long-term loyalty and engagement.
Customer Retention
Customer retention refers to the strategies and activities a company uses to prevent customer churn and encourage them to continue buying.
Dark Funnel
The Dark Funnel describes customer buying activities that are untrackable by companies, such as private chats and word-of-mouth referrals.
Data Appending
Data appending is the process of adding new data fields to your existing database records to enrich and complete your information.
Data Security
Data security protects digital information from unauthorized access, corruption, or theft throughout its entire lifecycle.
De-dupe
De-duping, or data deduplication, is the process of eliminating duplicate copies of data within a dataset to improve accuracy and save space.
Demand
Demand is the economic principle describing a consumer's desire and willingness to purchase a specific good or service at a particular price.
Demand Generation
Demand generation is the process of creating awareness and interest in your products to build a pipeline of qualified leads for your sales team.
Demand Generation Framework
A demand generation framework is a strategic process for creating awareness and interest in your product, ultimately driving new business.
Digital Advertising
Digital advertising is the practice of delivering promotional content to users through various online and digital channels like social media or search engines.
Direct Sales
Direct sales involves selling products directly to consumers in a non-retail setting, such as at home, online, or person-to-person.
Docker
Docker is a tool that packages applications and their dependencies into isolated environments called containers for easy deployment and scaling.
Dynamic Pricing
Dynamic pricing is a strategy where businesses set flexible prices for products or services based on current market demands and other factors.
Elevator Pitch
An elevator pitch is a short, memorable summary of what you do, designed to be delivered in the time it takes to ride an elevator.
Email Cadence
An email cadence is a scheduled sequence of emails sent to prospects over a specific period to nurture leads and drive engagement.
Email Marketing
Email marketing is a digital strategy where businesses send targeted emails to prospects and customers to build relationships and drive sales.
Email Personalization
Email personalization uses subscriber data—like their name, interests, or past behavior—to create highly relevant and targeted email campaigns.






















.png)